Best Cyber Security Software
Best cyber security software solutions include AppTrana, Check Point, Webroot SecureAnywhere, Netsparker Security Scanner, Astra Web Security, and CylancePROTECT. With several functionalities and advanced technology, these software solutions offer top-rated security against malware threats.



No Cost Personal Advisor
List of 20 Best Cyber Security Software
Emergents | 2024
All-in-One Vulnerability Management Tool
Vulnerability Manager Plus is renowned cyber security software. It includes a multi-OS compliance and vulnerability management solution with built-in remediation. It is a complete vulnerability management platform offering comprehensive coverage, meticulous evaluation, ongoing visibility, and holistic remediation of threats and vulnerabilities from a single console. Learn more about Vulnerability Manager Plus
Explore various Vulnerability Manager Plus features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Vulnerability Scanning
- Network Scanning
- Patch Management
- Risk Management
- Policy Management
- Vulnerability Assessment
- Prioritization
- Vulnerability Protection
Vulnerability Manager Plus Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Software by ESET
ESET Cybersecurity is a fully featured Security Awareness Training Software designed to serve Startups, SMEs, Enterprises. ESET Cybersecurity provides end-to-end solutions designed for Web App. This online Security Awareness Training system offers Security Awareness Training at one place. Learn more about ESET Cybersecurity
Explore various ESET Cybersecurity features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all ESET Cybersecurity Features- Security awareness training
ESET Cybersecurity Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Category Champions | 2024
Award winning antivirus software
BitDefender is one of the best cyber security software. The data-protection layer of Bitdefender's multi-layered ransomware defense system gives high protection to videos, documents, photos, and music from different types of ransomware assaults. Bitdefender Antivirus Plus immediately responds to e-threats without reducing the speed of any device. Bitdefender Antivirus Plus protects personal information and online privacy. Read BitDefender Reviews
Explore various BitDefender features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all BitDefender Features- Anti Spam
- VPN
- Cross-Platform Malware Detection
- Email Attachment Protection
- Email Alert
- Internet Security
- Safe Files
- Web Threat Management
Pricing
BitDefender Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Transform your data into secure tokens with Crypto
CryptoBind Data Security offers reliable cyber security software tools. CryptoBind Data Security offers a safe solution for producing digital signatures, generating encryption and signing keys, managing keys, and encrypting data. Advanced cryptographic and data security solutions from CryptoBind are designed expressly to safeguard sensitive information and satisfy legal compliance requirements. Learn more about CryptoBind Data Security
Explore various CryptoBind Data Security features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Risk Management
- Compliance Reporting
- Compliance Management
- Self Service Portal
- Financial Data Protection
- Application Security
- Tokenization
- Encryption
CryptoBind Data Security Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Software by Intruder
A cloud-based software used in cyber security, Intruder assists enterprises in automatically running security scans to find and address potential risks. Professionals can proactively monitor the system, get automated alerts about fresh vulnerabilities, and see how exposed they are to threats. Intruder enables businesses to give importance to critical issues and unify threat remediation processes by analyzing failed/passed checks, total checks, and inconsequential callouts. Learn more about Intruder
Explore various Intruder features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Intruder Features- Patch Management
- Risk Management
- Vulnerability Assessment
- Asset Tagging
- Network Scanning
- Prioritization
- Asset Discovery
- Vulnerability Scanning
Pricing
Essential
$ 38
Per Month
Pro
$ 180
Per Month
Verified
$ 450
Per Month
Intruder Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Category Champions | 2024
Antivirus software and spyware removal
Norton is one of the best software for cyber security. Norton Protection prevents the propagation and reproduction of malicious malware. Malware that replicates itself without using a host file is hindered by Norton protection. With multi-layered malware protection and new ways to safeguard devices and online privacy, Norton 360 gives device security to safeguard PCs, Macs, and mobile devices from viruses. Read Norton Reviews
Explore various Norton features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Norton Features- On-demand scans
- Privacy and security
- Privacy Protection
- Email Attachment Protection
- Delete/Repair infected files
- Detect viruses
- Desktop scans
- Desktop Notifications
Pricing
Standard
$ 10
Per Year
Norton Security Deluxe
$ 18
Per Year
Norton Security Premium
$ 39
Per Year
Norton Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Category Champions | 2024
McAfee for Consumer and Business
Premium antivirus program McAfee protects any kind of gadgets from online hazards and recognizes viruses in real-time. McAfee offers cyber security software tools that aid in supplementary services like a VPN, identity protection, PC cleaning, and disc shredding. Users may browse, shop, and conduct financial transactions with confidence because of unambiguous warnings of dangerous websites, links, and files provided by McAfee. Read McAfee Reviews
Explore various McAfee features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all McAfee Features- Privacy Protection
- Email Attachment Protection
- Spyware Removal
- Desktop Notifications
- IP Protection
- Anti Virus
- Delete/Repair infected files
- Event Tracking
Pricing
Total Protection
$ 50
Per Year
Internet Security
$ 80
Per Year
AntiVirus Plus
$ 60
Per Year
McAfee Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Software by Safer Social ltd
Perimeter 81 is a user-centric security measure that thwarts attempts to steal passwords. This software used in cyber security replaces multiprotocol labels by switching it with a secure web gateway. It employs SD-WAN to connect offices and uses a secure web gateway to protect online users. Businesses can easily migrate their resources to the cloud and obtain network insight from one cloud management site. Learn more about Perimeter 81
Explore various Perimeter 81 features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Perimeter 81 Features- Multi-Language
- Endpoint Management
- Kill Switch
- IP Protection
- Anonymous Browsing
- Two-Factor Authentication
- Multi-Protocol
- Whitelisting / Blacklisting
Pricing
Free
$ 0
month/team member
Business
$ 10
month/team member
Perimeter 81 Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Software by TotalAV, Inc
TotalAV is a well-known and reasonably priced antivirus program that scans devices for viruses and puts a stop to any incoming threats from being downloaded. This is one of the best cyber security software. A user-friendly and intuitive interface offers sophisticated real-time virus detection, good web security capabilities, and different data privacy measures. Learn more about TotalAV
Explore various TotalAV features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all TotalAV Features- Advanced Detection
- Remote Management
- Larger Files & More Storage
- Email Protection
- Smart Scanner
- Upload Portal
- Two-Factor Authentication
- Behavioral Analytics
TotalAV Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Unified SIEM tool and SOAR solution
Log360 is a security analytics tool that aids users in fending off threats in a hybrid, on-premises, or cloud environment. This cyber security software aids businesses in complying with regulations like PCI DSS, GDPR, HIPAA, and others. Users can alter the solution to suit particular use cases and safeguard private information. Learn more about ManageEngine Log360
Explore various ManageEngine Log360 features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Real Time Monitoring
- File Integrity Monitoring
- Audit Trails
- Network Monitoring
- Vulnerability Scanning
- IP Protection
- Endpoint Management
- AI / Machine Learning
ManageEngine Log360 Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Security solutions for SMBs and large enterprises
Acunetix is an automated platform that offers cyber security software tools for assessing web applications' security and auditing web apps for exploitable flaws like SQL Injection and Cross-Site Scripting. Any website or web application that can be accessed through a web browser and makes use of the HTTP/HTTPS protocol is easily scanned. Learn more about Acunetix
Explore various Acunetix features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Acunetix Features- IOC Verification
- Vulnerability Scanning
- Asset Tagging
- Asset Discovery
- Network Scanning
- Web Scanning
- File Access Control
- Database Security Audit
Acunetix Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Contenders | 2024
Software by Malwarebytes
Malwarebytes is one of the best cyber security software. Malwarebytes aid in scanning and removing viruses and malware from any kind of device. Its security can fend off ransomware and zero-day exploits, which are assaults that have never been seen before and which software makers haven't yet had a chance to patch. Read Malwarebytes Reviews
Explore various Malwarebytes features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Malwarebytes Features- Email Alert
- Detect viruses
- Desktop Notifications
- Online Protection
- Spyware Removal
- Delete/Repair infected files
- Privacy Protection
- Internet Usage Monitoring
Malwarebytes Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Contenders | 2024
Software by AVG Technologies
AVG Internet Security offers reliable cyber security software tools. It aids in protecting personal files, cameras, emails, and passwords from hackers. Users can shop and conduct financial transactions online without fear. The platform provides users with a quarantine area with contaminated data and the option to fix some virus-infected files. Read AVG Internet Security Reviews
Explore various AVG Internet Security features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Anti Virus
- Anti Spam
AVG Internet Security Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Contenders | 2024
Software by LogMeIn
LastPass is a popular software used in cyber security. Users of LastPass can keep their passwords safe in a virtual safe and use it for personal and professional purposes. It uses one-time authentication and password vaulting to protect user passwords. Users can import websites from their email accounts or other password manager applications as well. Read LastPass Reviews
Explore various LastPass features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all LastPass Features- User Activity Monitoring
- Access Request Management
- Account Management
- User Provisioning
- Password Reset
- Password Synchronization
- Role Management
- Credential Management
LastPass Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
One-stop solution for all your security needs
AppTrana is an all-inclusive cyber security software. Any web application can be deployed with its security firewall. AppTrana is a reliable website and application security solution that makes use of scanning, always-on security, risk identification, pen testing, traffic monitoring, WAF, and other modern techniques to help enterprises in handling and sustaining cloud security. Read AppTrana Reviews
Explore various AppTrana features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all AppTrana Features- Web Traffic Reporting
- Web Scanning
- Threat Protection
- Vulnerability Scanning
- Application Security
- Vulnerability Management
- Vulnerability Assessment
- Real Time Monitoring
Pricing
Premium
$ 399
Per Month
Advance
$ 99
Per Month
Basic
$ 0
Forever
AppTrana Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Category Champions | 2024
Software by Avast Software
Avast is a popular software used in cyber security. It offers protection from ransomware, phishing, Wi-Fi intrusion, and other cybersecurity risks, in addition to its protection against viruses and malware. Avast offers a wide range of features in addition to standard antivirus protection, including password protection, camera shield, data shredder, sandbox, etc. Read Avast Reviews
Explore various Avast features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all Avast Features- Privacy and security
- Ransomware Security
- Wi-Fi Security Scan
- Privacy Protection
- Desktop scans
- Anti-Malware Security
- Wi-Fi Intruders Alerts
- Fast Scanning
Avast Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Long-term data retention solution for businesses
The Mimecast Cloud Archive offers a consolidated, secure archive for email archiving, establishing a digital corporate memory while minimizing risk for legal and compliance teams. Mimecast offers cyber security software tools. The platform specializes in email security and offers a number of services to guard against risks, including spam, malware, and phishing. Learn more about Mimecast Cloud Archive
Explore various Mimecast Cloud Archive features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Compliance Management
- Backup Management
- Retention Management
Mimecast Cloud Archive Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
Best security software
VIPRE Security is one of the best cyber security software. Vipre Advanced Security aids in antivirus, firewall, and spam filtering. Threats are scanned for, and VIPRE Business Protection's anti-malware defenses guard against a variety of threats like Trojans, bots, rootkits, infections, and spyware. This solution also contains anti-phishing technology, blocking harmful websites and scanning portable devices. Learn more about VIPRE Security
Explore various VIPRE Security features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
VIPRE Security Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Emergents | 2024
NordLayer
NordLayer is a trustworthy software used in cyber security. It offers adaptable cybersecurity tools for companies of different sizes. IT departments will be able to manage security measures such as user authentication and verification using multifactor or biometric authentication and Single Sign-On (SSO), which is compatible with other top service providers. Learn more about NordLayer
Explore various NordLayer features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
Features
View all NordLayer Features- Mobile Authentication
- Biometric
- Anonymous Browsing
- Web Content Filtering
- Cloud Application Security
- Multi Protocol
- Web Inspection
- Peer to Peer
Pricing
Lite
$ 8
User/Month if chosen Yearly
Core
$ 11
User/Month if chosen Yearly
Premium
$ 14
User/Month if chosen Yearly
NordLayer Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Contenders | 2024
Software by Webroot Inc
Webroot is one of the best computer security software that finds endpoint protections. prevents internet issues and web-borne malware threats. Complete packaging with features i.e fast deployment, online arrangement, real-time data and offers intelligence stage. Immediate access at any time from anywhere. Read Webroot SecureAnywhere Reviews
Explore various Webroot SecureAnywhere features, compare the pricing plans, and unlock the potential of seamless operations by selecting the right software for your business.
- Privacy and security
- Small storage space
- Fast Scanning
- Anti-Phishing
- Desktop Notifications
- Security Event Log
- Real Time Monitoring
- Delete/Repair infected files
Webroot SecureAnywhere Caters to
- StartUps
- SMBs
- Agencies
- Enterprises
Cybersecurity has grown to be a top worry for people, companies, and organizations. Due to the frequency and sophistication of cyber threats, taking appropriate precautions to protect sensitive data, networks, and digital assets is essential. Cybersecurity software, which offers real-time detection, prevention, and response capabilities, is essential for protecting against a variety of cyber attacks.
Cybersecurity software offers comprehensive solutions to defend against ever-evolving cyber risks, from antivirus and firewall protection to advanced threat intelligence integration. In this dynamic landscape, staying up-to-date with the latest trends and selecting the right cybersecurity software is vital for maintaining a strong security posture.
What Is Cyber Security Software?
Cybersecurity software refers to a category of specialized applications and tools designed to protect computer systems, networks, and digital devices from various online threats and cyber-attacks. These dangers can be caused by spyware, ransomware, viruses, phishing scams, data breaches, and other destructive actions committed by online criminals.
The main purpose of cybersecurity software is to detect, prevent, and respond to these threats, ensuring the confidentiality, integrity, and availability of sensitive data and digital assets.
There are several types of cybersecurity software available, each serving different functions. Antivirus software is one of the most common types, focusing on identifying and removing known malware from devices and preventing new infections. The use of firewalls, which serve as a barrier between networks and the internet and monitor and regulate incoming and outgoing traffic to stop illegal access and potential attacks, is another crucial element.
Difference between Software Security and Cyber Security
Software security and cybersecurity are closely related concepts but have distinct focuses and scopes within the realm of digital protection -
-
Software Security
Software security primarily centers on ensuring the security and integrity of individual software applications and systems. It involves implementing measures and best practices to identify and mitigate vulnerabilities within the software's code and design. The main goal of software security is to prevent unauthorized access, data breaches, and exploitation of weaknesses that could lead to security compromises.
This involves steps like using secure coding techniques, validating input, implementing access controls, and updating software often to fix known security problems. Software security is a crucial aspect of the development lifecycle, as secure software forms the foundation of overall cybersecurity efforts.
-
Cybersecurity
Cybersecurity, on the other hand, encompasses a broader scope, focusing on protecting entire digital environments, including networks, computer systems, data, and connected devices, from a wide range of cyber threats.
It involves the implementation of strategies, technologies, and policies to defend against attacks, detect potential intrusions, and respond to security incidents. Cybersecurity addresses software security and includes hardware security, network security, cloud security, user awareness training, and incident response planning.
It takes into consideration the diverse and evolving threat landscape, which may include various forms of malware, social engineering attacks, DDoS attacks, ransomware, and more. Cybersecurity aims to safeguard critical assets, preserve privacy, and maintain business continuity.
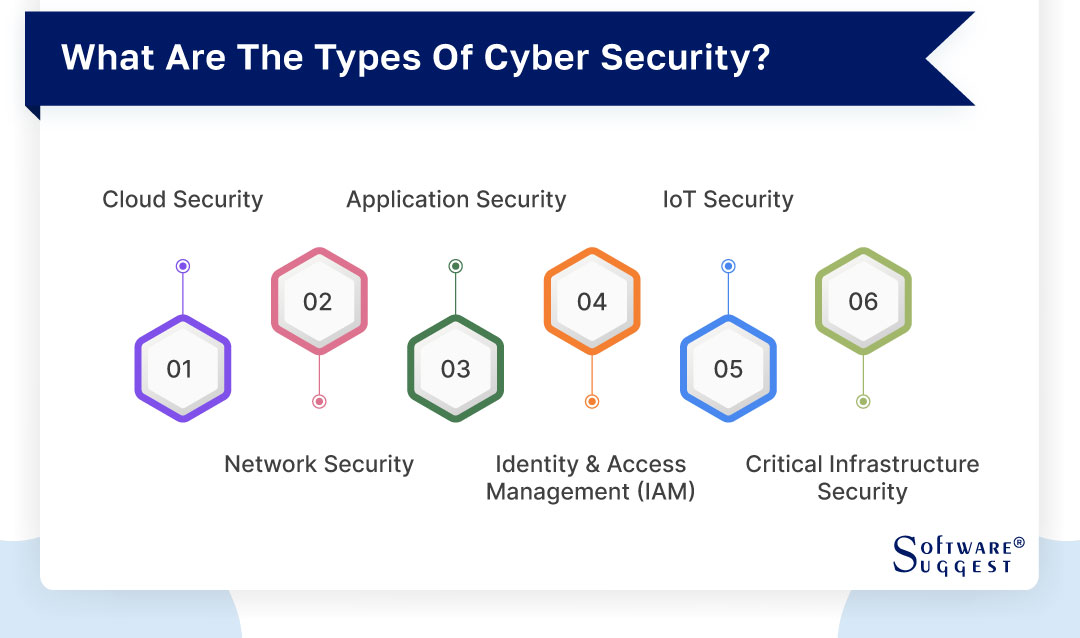
What Are the Types of Cyber Security?
Cybersecurity is a critical discipline that focuses on safeguarding digital systems, networks, and data from malicious activities and cyber threats. As technology continues to advance, the scope of cybersecurity has broadened to address various vulnerabilities across different domains. Here are some of the key types of cybersecurity that play crucial roles in ensuring the protection and integrity of our digital world:
-
Cloud Security
Cloud security is concerned with safeguarding data, applications, and services hosted on cloud platforms. As organizations increasingly adopt cloud computing to store and process sensitive information, protecting this data from unauthorized access and breaches becomes paramount. To secure the privacy and accessibility of data stored in the cloud, security measures include encryption, access limits, data segmentation, and ongoing monitoring.
-
Network Security
Securing the communication channels between systems and devices on a network within an organization is referred to as network security. It seeks to defend networks against unwanted access, data eavesdropping, and other online dangers. Network security tools, such as firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs), are utilized to identify and block malicious activities while allowing legitimate traffic to flow securely.
-
Application Security
Application security is concerned with finding and fixing flaws and vulnerabilities in software applications. To reduce the risk of being exploited by cyber attackers, secure coding methods, code reviews, and vulnerability assessments are used. By ensuring that applications are robust and free from vulnerabilities, organizations can mitigate the potential for data breaches and other security incidents.
-
Identity and Access Management (IAM)
IAM is concerned with overseeing and restricting user access to sensitive data and digital resources. It involves processes and technologies to authenticate users, grant appropriate access privileges, and monitor user activities. IAM helps prevent unauthorized access and identity-related security breaches, ensuring that only authorized personnel can access critical data and systems.
-
IoT Security (Internet of Things)
IoT security addresses the unique challenges presented by interconnected devices and objects within the Internet of Things ecosystem. With the proliferation of IoT devices in homes, industries, and critical infrastructure, securing these devices from cyber threats becomes crucial. IoT security measures involve authentication, encryption, and continuous monitoring to protect against the potential exploitation of IoT vulnerabilities.
-
Critical Infrastructure Security
Protecting critical systems and assets from cyber threats includes safeguarding power grids, transportation networks, and healthcare institutions. These infrastructures are crucial to the functioning of societies, and any disruption or breach could have severe consequences. Implementing robust cybersecurity measures helps prevent attacks that may lead to physical damage or disruption of essential services.
Types Of Cybersecurity Tools
The value of cybersecurity solutions in preserving sensitive data and defending against cyber threats has become clearer as the digital landscape changes. These tools play a crucial role in fortifying digital defenses, identifying vulnerabilities, and responding to potential security breaches. Here are some essential types of cybersecurity tools that organizations and individuals rely on to enhance their security posture -

-
Encryption Tools
Tools for encryption are essential for maintaining data secrecy. They use advanced algorithms to convert plaintext data into ciphertext, rendering it unreadable to unauthorized parties. Sensitive data is frequently protected during transmission and storage using encryption. Organizations can prevent cyber attackers from intercepting or accessing their data by using encryption techniques.
-
Antivirus Software
One of the most popular and fundamental cybersecurity tools is antivirus software.It is designed to discover, halt, and remove many types of malware, including viruses, Trojans, worms, and spyware. In order to provide real-time protection against possible threats, antivirus software continuously monitors systems and files for known malware signatures and suspicious activities.
-
Packet Sniffers
Data packets are tracked and analyzed as they go through a network using packet sniffers, also referred to as network analyzers. They aid cybersecurity experts in identifying potential attacks, finding network vulnerabilities, and doing network troubleshooting. These tools are normally utilized in a controlled environment by network administrators and security specialists due to the potential for malicious use.
-
Web Vulnerability Scanning Tools
Web application and website security flaws are evaluated using web vulnerability scanning technologies. These tools automatically identify potential entry points that attackers could exploit, such as SQL injection flaws, cross-site scripting (XSS) vulnerabilities, and insecure configurations. Web vulnerability scanning tools help organizations proactively address security gaps to prevent cyber attacks.
-
Network Security Monitoring Tools
tools for monitoring network security keep an eye on network traffic for nefarious or suspicious activity. These tools provide real-time alerts on potential threats, allowing security teams to respond quickly to security incidents. Network security monitoring is crucial for identifying and containing cyber threats before they cause significant damage.
-
Managed Detection and Response Services
Managed Detection and Response (MDR) services offer thorough threat detection and response by combining cutting-edge security technologies with human skills. MDR services offer continuous monitoring, threat hunting, incident response, and threat intelligence, making them a valuable resource for organizations lacking dedicated cybersecurity teams.
-
Penetration Testing
Penetration testing, commonly referred to as ethical hacking, simulates cyberattacks on a company's systems and networks in order to find weaknesses before malevolent hackers can take advantage of them. Penetration testing helps organizations understand their security weaknesses and implement appropriate measures to bolster their defenses.
-
Public Key Infrastructure Services
In order to manage digital certificates and encryption keys, PKI services are used. PKI plays a crucial role in ensuring secure communication and authenticating the identities of users and devices. PKI services are widely used to establish secure connections for tasks such as secure web browsing and encrypted email communication.
Types of Cybersecurity Threats
Cybersecurity hazards pose serious risks to both persons and organizations in the connected digital world of today. Cybercriminals always come up with new strategies to take advantage of flaws and obtain unauthorized access to critical information and systems. Understanding the various types of cybersecurity threats is crucial for implementing effective defense strategies. Here are some of the most common and concerning cybersecurity threats:
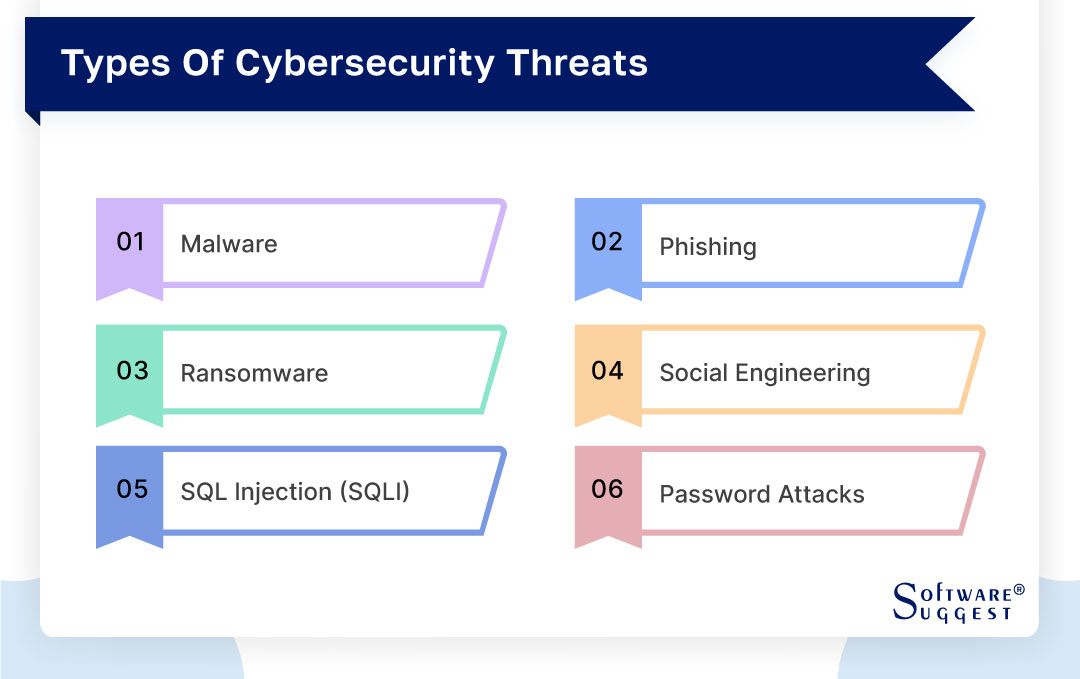
-
Malware
Malware, short for malicious software, refers to a broad category of software designed to cause harm to computers, networks, and devices. This contains malware such as spyware, adware, Trojans, and viruses. Malware can infect computers through phishing emails, vulnerable websites, or corrupt downloads. Malware can enter a system and steal confidential data, cause disruptions, or give hackers illegal access.
-
Phishing
The goal of phishing, a type of cyberattack, is to trick people into disclosing sensitive information like login passwords, credit card numbers, or personal information. Cybercriminals frequently use emails, texts, or websites to pretend to be reputable organizations like banks, social media sites, or government institutions. Unaware users could unwittingly submit information that is utilized for identity theft or other illegal activities.
-
Ransomware
A particularly sneaky kind of virus called ransomware encrypts a victim's files and makes them unavailable. The decryption key needed to open the files is typically provided in exchange for a ransom payment from cyber criminals. Ransomware attacks can have devastating consequences for individuals and businesses, leading to data loss and significant financial and operational damages.
-
Social Engineering
Social engineering is a non-technical type of cyber assault that uses psychological tricks to get people to reveal private information or do particular things. In order to win the target's trust, manipulation and deception are frequently used. Social engineering attacks, which include pretexting, baiting, and tailgating, can take many different forms and can be difficult to identify because they do not rely on conventional technological flaws.
-
SQL Injection (SQLi)
A form of web application vulnerability known as SQL Injection happens when online criminals use weak input validation in web applications to enter malicious SQL code into input fields. This may result in illegal database access, data tampering, and potential data breaches. SQLi attacks are particularly dangerous for web applications that process user input without proper validation and sanitation.
-
Password Attacks
Password attacks use a variety of methods to gain login information and passwords. Common methods include brute-force attacks, where attackers try all possible combinations to guess passwords, and dictionary attacks, which use a list of commonly used passwords. Password attacks can be successful when users have weak or easily guessable passwords, highlighting the importance of strong password practices and multi-factor authentication.
Benefits of Cyber Security Software
The importance of cybersecurity software cannot be emphasized at a time of rising digitalization and connectivity.Sensitive data, networks, and devices are at danger as a result of the continual evolution of cyber threats.
Implementing robust cybersecurity software solutions is crucial for organizations and individuals alike to defend against these threats and safeguard their digital assets. Here are some of the key benefits that cybersecurity software offers:

-
Improved Data Security
Cybersecurity software provides a strong defense against unauthorized access and data breaches. These solutions protect sensitive information from cybercriminals by encrypting data, putting access limits in place, and keeping an eye out for unusual activity.
-
Threat Detection and Prevention
Network traffic, system logs, and user activity are continuously monitored by cybersecurity software to identify and immediately stop any potential threats. Advanced threat detection algorithms and machine learning capabilities enable early identification of malware, viruses, and other malicious activities, preventing cyber attacks before they can cause significant harm.
-
Vulnerability Assessment
Cybersecurity software conducts regular vulnerability assessments to identify weaknesses in systems and applications. By pinpointing potential security gaps, organizations can proactively address these vulnerabilities and minimize the risk of exploitation by cyber attackers.
-
Incident Response and Recovery
In the event of a cyber attack, cybersecurity software plays a crucial role in facilitating rapid incident response and recovery. These tools help contain the breach, mitigate its impact, and restore systems and data to normal operation, minimizing downtime and losses.
-
Better Compliance Management
Many industries are subject to strict data protection and cybersecurity regulations. Cybersecurity software assists organizations in meeting compliance requirements by ensuring the implementation of necessary security measures and maintaining detailed audit logs and reports.
-
Protection of IoT Devices
As the Internet of Things (IoT) expands, the security of connected devices becomes paramount. Cybersecurity software helps protect IoT devices from potential exploitation by cybercriminals, preventing unauthorized access and ensuring the privacy and safety of users.
-
Firewall Protection
Between an organization's internal network and the internet, firewall software serves as a barrier by regulating incoming and outgoing traffic. It blocks unauthorized access attempts and filters out potentially harmful data packets, providing an essential layer of protection against external threats.
-
User Authentication
To ensure that only authorized people can access sensitive systems and data, cybersecurity software incorporates strong user authentication techniques like multi-factor authentication (MFA). Even if passwords are compromised, this stops unauthorized parties from gaining access.
Features of Cyber Security Software
In order to protect digital systems, data, and networks from a variety of cyber threats, cybersecurity software is essential. These software solutions come equipped with a diverse set of features that work together to provide comprehensive protection against malicious activities. Let's explore in detail some of the key features offered by cybersecurity software:
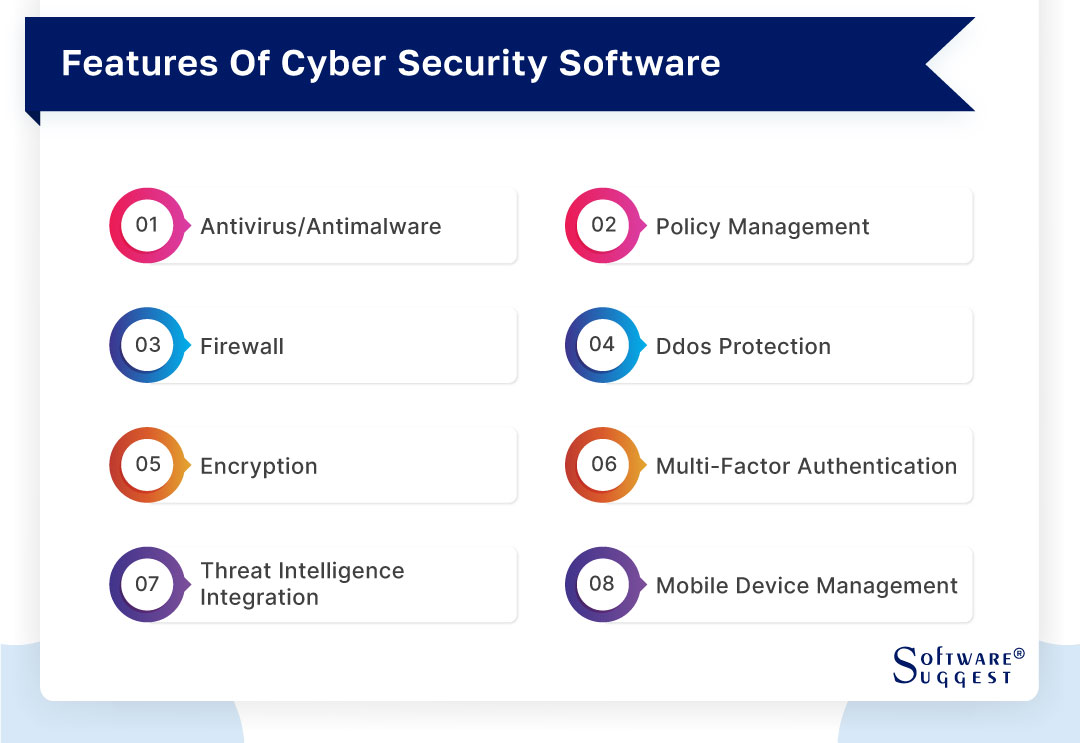
-
Antivirus/Antimalware
Antivirus and antimalware functionalities are foundational features of cybersecurity software. These tools continuously scan files, emails, and web content for known viruses, malware, Trojans, and other malicious software. When a threat is detected, the software takes immediate action to quarantine, neutralize, or remove the malicious code, preventing it from causing further harm to the system.
-
Policy Management
Policy management features enable organizations to enforce consistent security policies and configurations across their entire network. Cybersecurity software allows administrators to define rules and access controls, ensuring that all devices and systems adhere to security standards.By doing so, possible vulnerabilities are reduced and industry standards and best practices are followed.
-
Firewall
The firewall feature serves as a wall separating the internal network of a business from the internet.It is possible to filter out unwanted access and potentially harmful data packets by inspecting incoming and outgoing network traffic. For defense against external threats like hacking attempts and infiltration attempts, firewalls are crucial.
-
DDoS Protection
Distributed Denial of Service (DDoS) attacks are a common method used by cybercriminals to disrupt online services by overwhelming servers with a massive influx of traffic. Cybersecurity software with DDoS protection can detect and mitigate these attacks, ensuring the continuous availability of websites and online resources.
-
Better Compliance Management
Sensitive data must be protected both during transmission and storage by using encryption. Strong encryption methods are used by cybersecurity software to transform plaintext data into ciphertext, rendering it unreadable by unauthorized users. Even if intercepted, encrypted data remains secure, ensuring data confidentiality and privacy.
-
Multi-Factor Authentication (MFA)
By requiring several forms of identification before giving access to sensitive systems or data, MFA improves the security of user authentication. This frequently requires a combination of the user's knowledge (password), possessions (a smartphone or hardware token), and/or identity (facial or fingerprint identification).The risk of unauthorized access brought on by compromised or stolen credentials is significantly reduced with MFA.
-
Threat Intelligence Integration
Threat intelligence integration is a vital component of cybersecurity software. It updates the software with the most recent online dangers and attack patterns.. By incorporating real-time threat intelligence feeds, the software can proactively identify and defend against emerging threats, giving organizations a more proactive and adaptive security posture.
-
Mobile Device Management (MDM)
In an era of widespread mobile device usage, MDM features have become essential for organizations. MDM enables managers to enforce security guidelines, centrally monitor and safeguard mobile devices, and remotely delete data in the event of loss or theft. In addition to protecting sensitive data on mobile devices, this ensures compliance with security standards.
How to Choose the Right Cyber Security Software?
In today's digital landscape, choosing the right cybersecurity software is paramount for organizations and individuals seeking to protect their data and systems from cyber threats. It might be difficult to choose the best cybersecurity software when there are so many options available.
Several crucial things must be taken into consideration to provide an efficient protection against cyberattacks. Here's a detailed guide on how to choose the right cybersecurity software:

-
Functionality/Multiple Security Features
Assess the functionality of the cybersecurity software and ensure that it offers a comprehensive set of security features. Look for antivirus/antimalware protection, firewall capabilities, encryption, intrusion detection, and other essential functionalities. Choosing software that integrates multiple security features ensures a layered defense against various cyber threats.
-
Scalability
Think about how scalable cybersecurity software is. The software should be able to accommodate growing data and user demands without sacrificing security as your firm expands. In the long run, a scalable solution will save time and resources by preventing the need for constant software replacement.
-
Compatibility
Check the compatibility of the cybersecurity software with your existing systems and infrastructure. Ensure that it integrates seamlessly with your operating systems, network equipment, and other software applications. Compatibility issues could lead to operational disruptions and gaps in security coverage.
-
Support and Customer Service
Reliable support and customer service are crucial when choosing cybersecurity software. Opt for a vendor that offers timely and responsive support, including help with installation, configuration, and troubleshooting. This ensures that any issues or concerns are addressed promptly to maintain optimal security.
-
Industry Certifications and Compliance
Look for cybersecurity software that holds industry certifications and compliance with relevant standards and regulations. Certifications such as Common Criteria, ISO 27001, and NIST compliance indicate that the software meets stringent security and quality requirements.
-
Trial and Testing
Consider software that offers a trial or testing period. This allows you to evaluate the software's performance and suitability for your specific needs. During the trial, test the software's features, compatibility, and user-friendliness to ensure it aligns with your cybersecurity requirements.
-
Cost and Budget
Evaluate the total cost of ownership of the cybersecurity software, including licensing fees, maintenance, and support. Consider your budget and determine the value the software provides in relation to its cost. While cost is essential, prioritize the overall effectiveness and suitability of the software over the price tag.
List of Top 5 Cyber Security Software Tools Comparison
|
Name
|
Free Trial
|
Demo
|
Pricing
|
|---|---|---|---|
|
30 Days |
Yes |
Starting price at $16.66/month |
|
|
14 Days |
Yes |
Premium + Privacy VPN (5Devices): $8.33/month |
|
|
7 Days |
Yes |
On Request |
|
|
7 Days |
Yes |
On Request |
|
|
30 Days |
Yes |
On Request |
Having the appropriate cybersecurity software tools is crucial for protecting sensitive data and networks in the always-changing arena of cyber threats. Numerous cybersecurity solutions are available on the market, each with special characteristics to handle particular security issues. Here is a list of the top five cybersecurity software solutions, chosen for their potency and all-around security -
1. McAfee
The main goal of McAfee is to offer security solutions that shield mobile devices, networks, and computer systems from numerous cyber threats like viruses, malware, ransomware, spyware, and other online dangers. To locate and eliminate established and new threats, the program combines signature-based and behavioral detection techniques.
Over time, McAfee has increased the number of products it offers, including those that are specifically suited for home users, small businesses, enterprises, and governmental institutions. These solutions usually contain capabilities like real-time scanning, firewall security, email security, internet protection, and vulnerability detection, to name just a few.
- Virus and malware protection
- Firewall protection
- Email security
- Web protection
- Vulnerability scanner
- Identity theft protection
- Safe online banking and shopping
- Password Manager
- Parental controls
- Device optimization
- Cloud-based management
- Multi-device support
- The software has a feature that notifies instantly when it finds a threat or potential threat.
- The tool is very useful for mobile devices and laptops.
- The tool is user-friendly and simple to use.
- The random McAfee popups can be annoying.
- Sometimes it blocks websites when needed to use for work as being potentially harmful.
- Scanning features can sometimes take a while.
Pricing
- McAfee + Ultimate: $199.99/year
- McAfee + Advanced: $89.99/year
- McAfee + Premium: $49.99/year
- Essential: $39.99/year
2. Malwarebytes
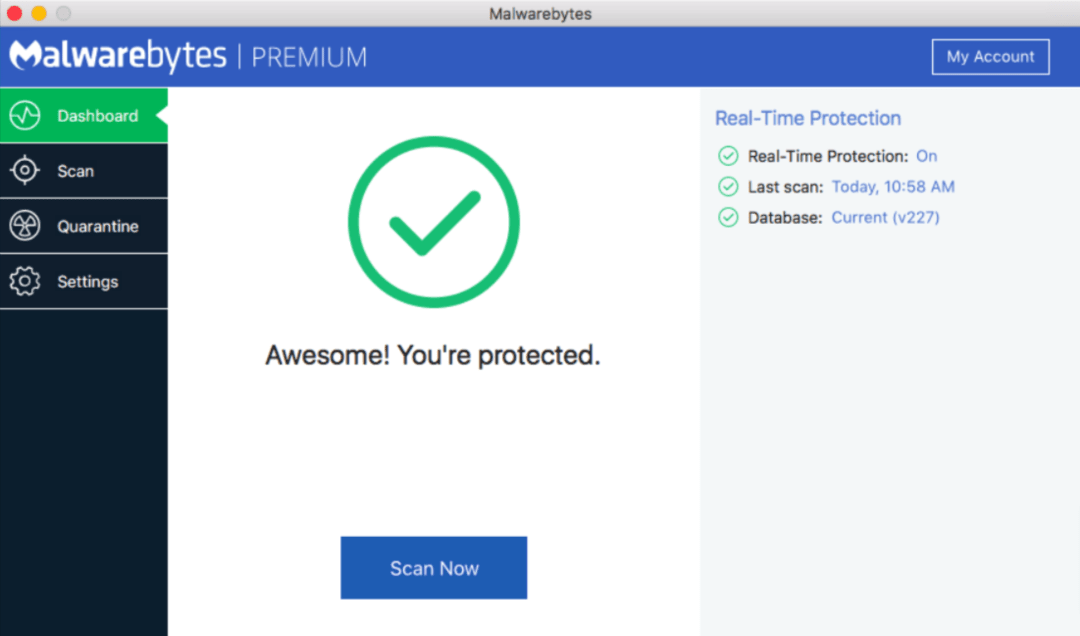
Malwarebytes is the best software for cyber security that specializes in providing protection against various forms of malware. The software's main selling point is how strongly it emphasizes the identification and removal of viruses. Advanced heuristic analysis and behavior-based monitoring are used to detect and eliminate a variety of malware, such as viruses, worms, Trojan horses, spyware, adware, and ransomware.
Malwarebytes is designed to work alongside traditional antivirus software or as a standalone solution, offering an additional layer of defense against evolving and sophisticated cyber threats. Its ability to target and eliminate malware that may bypass other security measures has earned it a loyal user base.
- Malware detection and removal
- Real-time protection
- Web protection
- Anti-exploit Technology
- Ransomware protection
- Malicious website blocking
- Behavior monitoring
- Scheduled scans
- Quarantine
- Customizable scan options
- Chameleon technology
- Automatic updates
- The weekly reports help to check which employees are not being careful in the emails they open or programs they run.
- Malwarebytes will warn the team if a website does not look safe.
- The software's admin console is great because it is easy to use and understand.
- The software should have more options for types of scans to run.
- Auto updates fail at times in the software.
- Reporting could be a little more robust and having the ability to drill down would be nice.
Pricing
- Premium + Privacy VPN (5Devices): $8.33 per month
- Premium + Privacy VPN (3Devices): $6.67 per month
- Premium (5Devices): $5 per month
3. Check Point
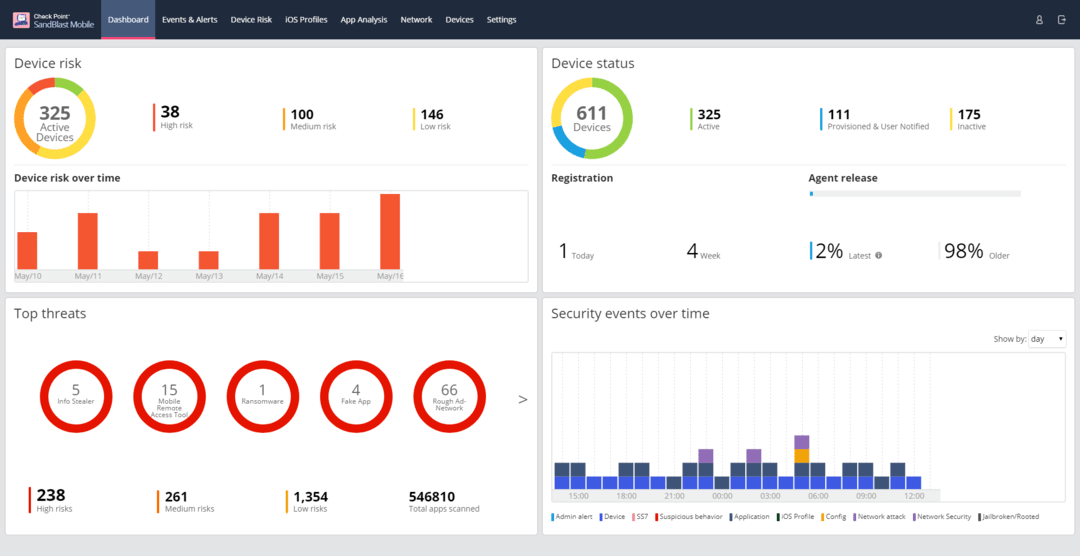
Check Point, a renowned cybersecurity software provider established in 1993, has emerged as a prominent force in the industry by delivering comprehensive security solutions tailored to safeguard enterprises and organizations from a myriad of cyber threats.
The company's extensive portfolio comprises a diverse array of software and networks from sophisticated cyberattacks. Thanks to their tailored approach, Check Point's products cater to the specific security demands of enterprises, governments, and small to medium-sized businesses alike.
- Firewall protection
- Threat prevention
- Network security
- Cloud security
- Endpoint protection
- Security management
- Threat intelligence
- Security automation
- Mobile security
- Compliance and reporting
- The management console is very easy to use.
- The team has the capacity to control particular websites or IP addresses based on predetermined web content or monitor specific end users.
- The support for Check Point is excellent.
- Check Point has a complex range of reporting tools, some of which can take time to learn and be comfortable with.
- The firewall is solid and needs to have someone with training to manage it which means any little mistake can bring down the network.
- The software is expensive.
Pricing
- On Request
4. Norton AntiVirus
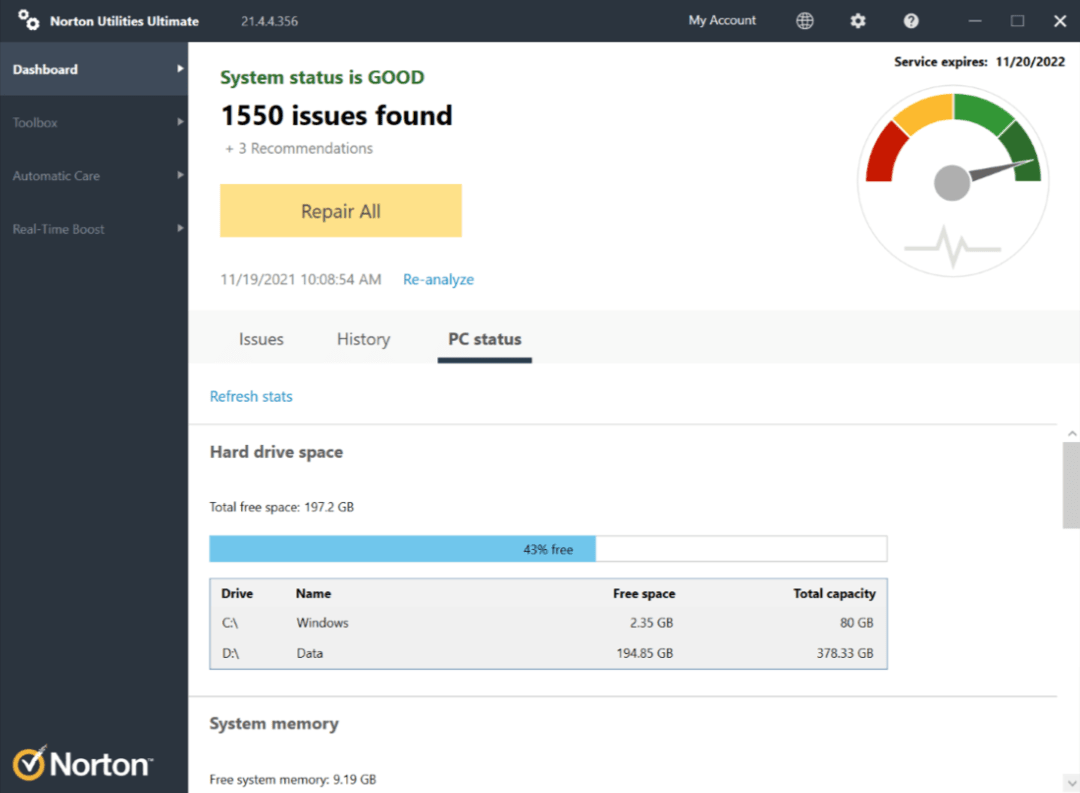
Norton AntiVirus is a well-known and widely used cybersecurity software developed by NortonLifeLock, a leading cybersecurity company. Norton AntiVirus is made to defend computers and other electronic devices against a range of online dangers, such as viruses, malware, spyware, ransomware, and phishing scams. With a history dating back to the early 1990s, Norton AntiVirus has established itself as a trusted and reliable antivirus solution. The software uses signature-based detection and advanced heuristics to identify and eliminate known and emerging threats in real-time, ensuring that users' devices remain secure.
- Malware and virus scans.
- Real-time threat protection
- Smart Firewall
- PC cloud backup
- Parental controls
- Password Manager
- Secure VPN
- System optimization
- Malware scanning
- Real-time protection
- Web protection
- Email security
- Firewall protection
- Automatic updates
- Device optimization
- Norton is a completely clean-to-apply software program that gives many capabilities and options.
- Antivirus is included, and protection features are always up-to-date.
- Norton works quite quickly and is efficient enough to detect threats.
- It is very easy and simple to install and is without any complications and irrelevant inquiries.
- Customer service is not immediate.
- Poor performance against Spyware and other threats
- There is Regular blocking of incoming scripts.
- Little or almost no compatibility with the Windows XP Firewall, but they are involved.
Pricing
- On Request
5. Avira

Avira is a well-known provider of cybersecurity software that offers a variety of security solutions to shield devices and computer systems from online dangers. Founded in 1986, Avira has a long history of offering effective antivirus and internet security products to both individual users and businesses. Avira's cybersecurity software is known for its robust malware detection and removal capabilities. The program uses sophisticated scanning methods, such as behavior-based and signature-based analysis, to locate and eliminate different kinds of malware, including viruses, Trojan horses, worms, spyware, and ransomware.
- Malware detection and removal
- Real-time protection
- Web protection
- Email security
- Firewall protection
- Device optimization
- USB drive protection
- Identity protection
- Network scanner
- Automatic updates
- Parental Control
- Gaming mode
- The software's scanning engine is advanced and doesn't consume much time in scanning.
- It is a highly effective tool against spam.
- All the features of the software work perfectly.
- Its interface is hard for beginners.
- Its backup module needs improvement and advancement.
- There should be a system to block pop-ups and ads permanently.
Pricing
- On Request
Challenges of Cybersecurity Software
In the face of an increasingly complex and dynamic cyber threat landscape, cybersecurity software is critical in protecting digital assets and networks. However, these software solutions also encounter various challenges that must be addressed to maintain effective security. Understanding these challenges is essential for organizations and individuals seeking to strengthen their cybersecurity defenses. Here's a detailed description of the key challenges faced by cybersecurity software -

-
Sophisticated and Evolving Threats
Cybercriminals continuously develop sophisticated attack techniques, making it challenging for cybersecurity software to keep up with the ever-changing threat landscape. Malware variants, ransomware strains, and other malicious tools evolve rapidly, often bypassing traditional security measures and demanding advanced detection and prevention capabilities.
-
False Positives and Negatives
Cybersecurity software may occasionally produce false positives, mistakenly flagging legitimate activities as malicious. These false positives can lead to disruptions in business operations and create frustration for users. Conversely, false negatives occur when the software fails to detect actual threats, leaving organizations vulnerable to potential cyber-attacks.
-
Insider Threats
Cybersecurity software often focuses on external threats, but insider threats pose a significant challenge. Traditional security measures can be circumvented by the malicious or careless employee or trusted insider behavior, resulting in data breaches and the compromise of sensitive data.
-
Continuous Updates and Patching
Maintaining up-to-date cybersecurity software is crucial, as it ensures protection against newly identified threats. Regular patching and upgrades, however, can be time- and resource-consuming, particularly for large-scale deployments. Failure to update promptly could leave systems vulnerable to known exploits.
-
Vendor and Supply Chain Risks
Organizations often rely on third-party vendors and software components, introducing supply chain risks. Cybersecurity software could be compromised through vulnerabilities or backdoors in the supply chain, potentially providing attackers with access to the entire network.
-
Emerging Technologies and Trends
The rapid adoption of emerging technologies, such as the Internet of Things (IoT), artificial intelligence, and cloud computing, introduces new security challenges. Cybersecurity software must adapt to the unique vulnerabilities and threats associated with these technologies to provide adequate protection.
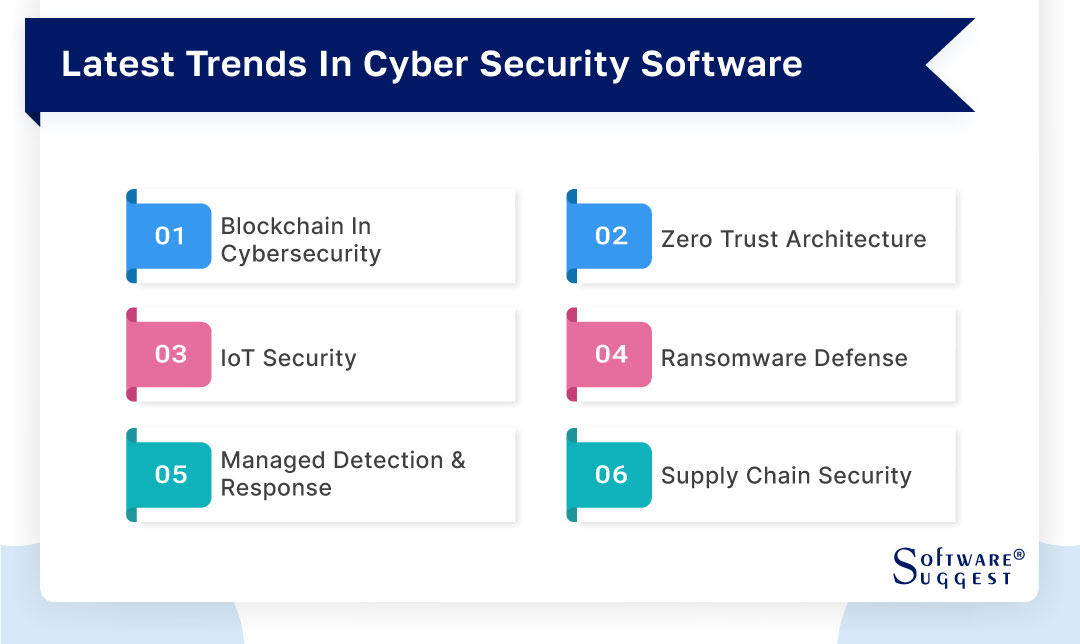
Latest Trends in Cyber Security Software
The area of cybersecurity is always evolving to address new threats and issues as the digital environment changes. In order to protect sensitive data and systems from criminal activity, cybersecurity software is crucial. In this dynamic environment, staying up-to-date with the latest trends in cybersecurity software is essential. Let's explore some of the most recent trends shaping the industry -
-
Blockchain in Cybersecurity
Blockchain technology is gaining traction in cybersecurity due to its decentralized and immutable nature. It offers enhanced data integrity, making it difficult for cyber attackers to tamper with records. By leveraging blockchain, cybersecurity software can provide secure authentication, secure data sharing, and improved identity management, reducing the risk of data breaches and unauthorized access.
-
Zero Trust Architecture
A security architecture called Zero Trust Architecture (ZTA) makes no assumptions about the reliability of any person or device, even if they are connected to the organization's network. Before allowing access, this method checks and validates each access request. In order to ensure that only authorized parties can access sensitive resources, cybersecurity software built on ZTA continuously authenticates users and devices.
-
IoT Security
As the Internet of Things (IoT) continues to expand, IoT security becomes a significant concern. Cybersecurity software is adapting to address the unique challenges of securing interconnected devices. It employs encryption, authentication, and continuous monitoring to protect IoT devices and networks from potential exploitation.
-
Ransomware Defense
The rise of ransomware attacks has pushed cybersecurity software to focus on robust ransomware defense mechanisms. AI-driven ransomware detection, behavior-based analysis, and enhanced backup and recovery solutions are employed to detect, block, and recover from ransomware attacks more effectively.
-
Managed Detection and Response (MDR)
Managed Detection and Response (MDR) services offer thorough threat detection and response by combining cutting-edge cybersecurity technologies with human skills. MDR services offer continuous monitoring, proactive threat hunting, and rapid incident response, ensuring timely and effective mitigation of cyber threats.
-
Supply Chain Security
Supply chain security has become a critical concern as cyber attackers increasingly target third-party vendors and components. Cybersecurity software now integrates supply chain security features to assess and monitor the security posture of third-party partners, reducing the risk of supply chain-related breaches.
Pricing Information of Cyber Security Software
The pricing of cybersecurity software varies widely depending on the specific features, functionalities, and scale of deployment required.
Basic antivirus software for individual users can range from free versions with limited features to premium subscriptions with annual fees ranging from $20 to $100 per user.
For small to medium-sized businesses, comprehensive cybersecurity suites typically cost between $50 to $150 per user per year, offering a broader range of features such as firewall, encryption, and multi-factor authentication.
Enterprise-grade cybersecurity solutions are more customizable, with pricing based on the number of users and the extent of network coverage, often ranging from a few thousand to several hundred thousand dollars annually. Additional costs may also include maintenance, support, and regular updates to ensure the software remains effective against evolving threats.
Conclusion
As cyber threats continue to evolve, the significance of cybersecurity software has never been more critical. From individual users to large enterprises, the need to safeguard sensitive data and digital operations against malicious activities remains paramount. Cybersecurity software provides a comprehensive defense, combining cutting-edge technologies, proactive threat detection, and continuous updates to mitigate risks effectively.
It enables organizations and individuals to confidently navigate the digital landscape, knowing that their data and networks are protected from the growing complexity of cyber attacks. By making informed decisions, staying vigilant, and embracing the latest advancements in cybersecurity software, we can fortify our digital environments and ensure a secure and resilient digital future.
Related Articles
FAQs
An intentional and hostile attempt to compromise, exploit, or disrupt digital systems, networks, or devices is known as a cyber attack. To gain unauthorized access, steal confidential information, jeopardize data integrity, or obstruct regular business, cybercriminals employ a variety of tactics and methods. Malware infections, phishing schemes, DoS assaults, ransomware, and social engineering techniques are examples of common cyberattack types. Cyber attacks can have a variety of purposes, such as monetary gain, intellectual property theft, political aspirations, or just general chaos and disruption.
Several programming languages are commonly used in cybersecurity to develop and implement various security tools, applications, and solutions. Some of the primary programming languages utilized in this field include:
- Python
- C/C++
- Java
- JavaScript
- Ruby
- Go
- PowerShell
The length of time needed to study cybersecurity varies depending on a person's background in technology, prior knowledge, and level of competence wanted. It may take several months of committed study and practice for someone with a rudimentary understanding of computer systems and networking to acquire essential cybersecurity abilities. This could involve online courses, self-study, hands-on lab exercises, and participation in cybersecurity communities.
NGFW stands for Next-Generation Firewall in cybersecurity. It is an advanced type of firewall that goes beyond traditional packet filtering and stateful inspection. NGFWs incorporate additional security features such as intrusion prevention, application awareness and control, deep packet inspection, and SSL decryption. These capabilities enable NGFWs to provide more comprehensive protection against modern cyber threats, including advanced malware, ransomware, and targeted attacks. NGFWs are designed to offer enhanced visibility and control over network traffic, allowing organizations to strengthen their security posture and effectively defend against sophisticated cyber attacks.
Yes, cybersecurity is generally considered a well-paid profession. Salary levels in the cybersecurity industry have increased as a result of the growing demand for qualified cybersecurity specialists in response to the growing number of cyber threats and attacks. The complexity and criticality of the work involved, coupled with the need for specialized skills and knowledge, contribute to higher earning potential.
By Industries